The hacking of Linux Mint - And out came the wolves
By now most people have gotten up to speed with latest news regarding the attack against the Linux Mint infrastructure and the ripples it created within the Mint community. If not, here is yet another quick and superficial recap:
- The Linux Mint website was compromised.
- The Mint forum database containing 145k accounts was sold online.
- The Mint 17.3 Cinnamon edition was reassembled and bundled with malware.
Obviously not a good week for the Mint team, and predictably enough they are getting truckloads of fud flung their way. While they do deserve some flack, it seems far fetched to claim that the perceived lack of security with the Mint distribution translates into this week’s disaster.
What is the security issue with Mint?
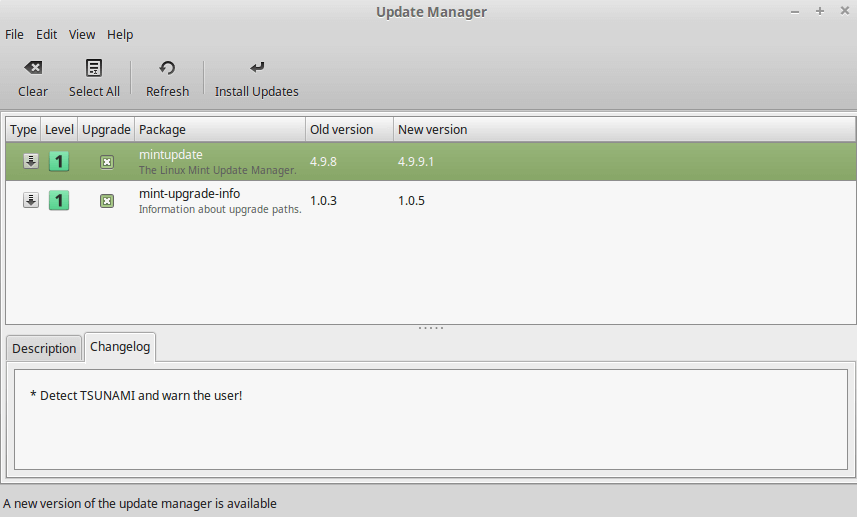
The Update Manager hunting malware.
If you’re unfamiliar with the “debate” regarding lack of security with the Mint distribution, it originates from Mint’s policy to hold back updates (security related or not) for packages that Mint deem as a threat to system stability. On that list we’ll find the kernel, xorg, systemd, grub2 and more. Check the mint update rules for details (level 4 & 5).
I personally find this particular policy very unfortunate but it should be mentioned that Mint leaves the final decision on weather or not to patch those “blocked packages” to the end user.
Let’s everybody blame WordPress
The Mint team was very open about how their website was compromised.
Yes, the breach was made via wordpress. From there they got a www-data shell.
- Clement Lefebvre
WordPress was without doubt the downfall of Mint according to several YouTube based (Linux) security experts, proclaiming WordPress a free meal for any script kiddie. Interestingly enough, none of the experts seemed to consider that a php shell inside a compromised WordPress installation should never compromise the server. If that was usually the case, nobody would be doing WordPress installations on shared hosting. In short, if a WordPress exploit compromised the entire server, then the Linux Mint crew needs to hire a sysadmin.
Doubts regarding the origin of the security breach
On January 16th @ChunkrGames tweeted that the Mint database was for sale on several forums, he even included a screenshot documenting the breach. The screenshot in question depicts the infamous PHP based WSO shell, and yeah it’s as bad as it looks. Even though Mint was tagged by their Twitter handle, they seem to have missed the mention altogether. I’ve since seen no comment from the Mint crew regarding this essential information.
The good, the bad and the ugly
What Mint did right:
- Went public and kept their userbase up to date.
- Informed their users on how to identify the compromised ISO.
- Eventually reached out to security experts to build a more secure infrastructure.
What Mint (probably) did wrong:
- Did not use a Web Application Firewall.
- Did not aptly secure critical services from intrusion attempts.
- Did not implement the use of secure passwords.
- Did not sufficiently monitor traffic and services.
- Did not offer HTTPS to their users.
- Prematurely put the website back online before they had identified critical vulnerabilities.
Whats next for Linux Mint
As one of the most popular Linux distributions with a large community I’m sure people will eventually forgive and forget. People today sadly expect that web services will be compromised and that personal information will be leaked under the notion of that’s what you get for playing on the Internet. As for Linux Mint, I’m sure they will resurface with an improved infrastructure and a renewed focus on security.
As a side note, one should also consider that the security flaws exposed by the Linux Mint breach might seem discouraging from a user point of view. However, I can assure you that IT professionals are much better at giving others advice than to follow best practices themselves. There, I’ve told you the truth, now we can all sleep much better at night ;-)
Sources: This article is based entirely on information provided through the Linux Mint blog and the coverage done by zdnet.com.