Jorgee goes on a rampage
In a time-frame of just 10 seconds I got 1200 requests from the Jorgee vulnerability scanner, originating from 15 unique IP addresses. As usual it was just a blind attack probing a /24 subnet.
I deploy a rather aggressive ModSecurity with Fail2ban defense that banned every offending IP address within a few seconds. Still, I must admit that 1200 requests slipping through the cracks was a bit more than expected. I guess my RPi3 can’t really go toe to toe against Digital Ocean and other cloud based hosting providers.
Even if you don’t deploy a web application firewall it’s still easy to block these types of attacks with the Apache mod_rewrite module. Every single request followed the same pattern:
104.131.252.112 - - [01/Apr/..] "HEAD http://109.109..:80/phpMyAdmin/ HTTP/1.1" 403 - "-" "Mozilla/5.0 Jorgee"
User agent:
“Mozilla/5.0 Jorgee” => The attacker is polite and informs us it’s actually Jorgee, well known vulnerability scanner. We can simply block this attack by identifying “Jorgee” from its user agent string:
# Block bad user agents
<IfModule mod_rewrite.c>
RewriteCond %{HTTP_USER_AGENT} ^.*(jorgee|morfeus|other).* [NC]
RewriteRule ^(.*)$ - [L,R=403]
</IfModule>
Host header:
http://IPADDRESS:PORT => A blind scan of IP addresses, at best performed against a block of static IP addresses. We’ll be less vulnerable against these sorts of attacks by not accepting numeric or unknown host headers:
# Block unwanted host headers
<IfModule mod_rewrite.c>
RewriteCond %{HTTP_HOST} !^blog\.paranoidpenguin\.net$ [NC]
RewriteCond %{HTTP_HOST} !^www\.blog\.paranoidpenguin\.net$ [NC]
RewriteRule ^(.*)$ - [L,R=403]
</IfModule>
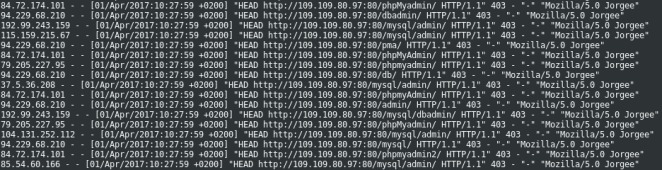
A Jorgee vulnerability scan in progress.
The list of attacking IP addresses:
104.131.252.112 115.159.215.67 123.206.107.228 155.133.45.237 192.99.243.159 37.188.113.215 37.5.36.208 62.197.125.167 62.231.98.228 79.160.64.5 79.205.227.95 84.72.174.101 85.54.60.166 94.229.68.210